The $96 Million Wake-Up Call
In May 2024, Synapse Financial Technologies – a Banking-as-a-Service middleware provider serving over 100 fintech programs – filed for bankruptcy. The fallout was not abstract. Between $85 million and $96 million in end-user funds went missing. Over 100,000 customers lost access to their accounts. The FDIC, designed to protect depositors, could not intervene effectively because the failure occurred not at the bank level but in the middleware layer – the BaaS platform itself.
Synapse’s collapse was not a black swan. It was the predictable consequence of a structural flaw: an entire ecosystem of fintechs had built their businesses on infrastructure they did not own, could not audit, and could not operate independently. When the single point of failure broke, there was no fallback.
This paper argues that the Synapse disaster, and the wave of regulatory responses it triggered, reveal a fundamental truth about fintech infrastructure: the distribution model matters more than the feature set.
Specifically, we demonstrate that among the four dominant models for distributing fintech infrastructure – pure SaaS, managed cloud, open source, and source code licensing – only source code access fully eliminates vendor lock-in risk.
This is not a theoretical argument. It is an operational imperative backed by regulatory mandates now taking effect across the United States, the European Union, and the Middle East.
Four Models, Four Risk Profiles
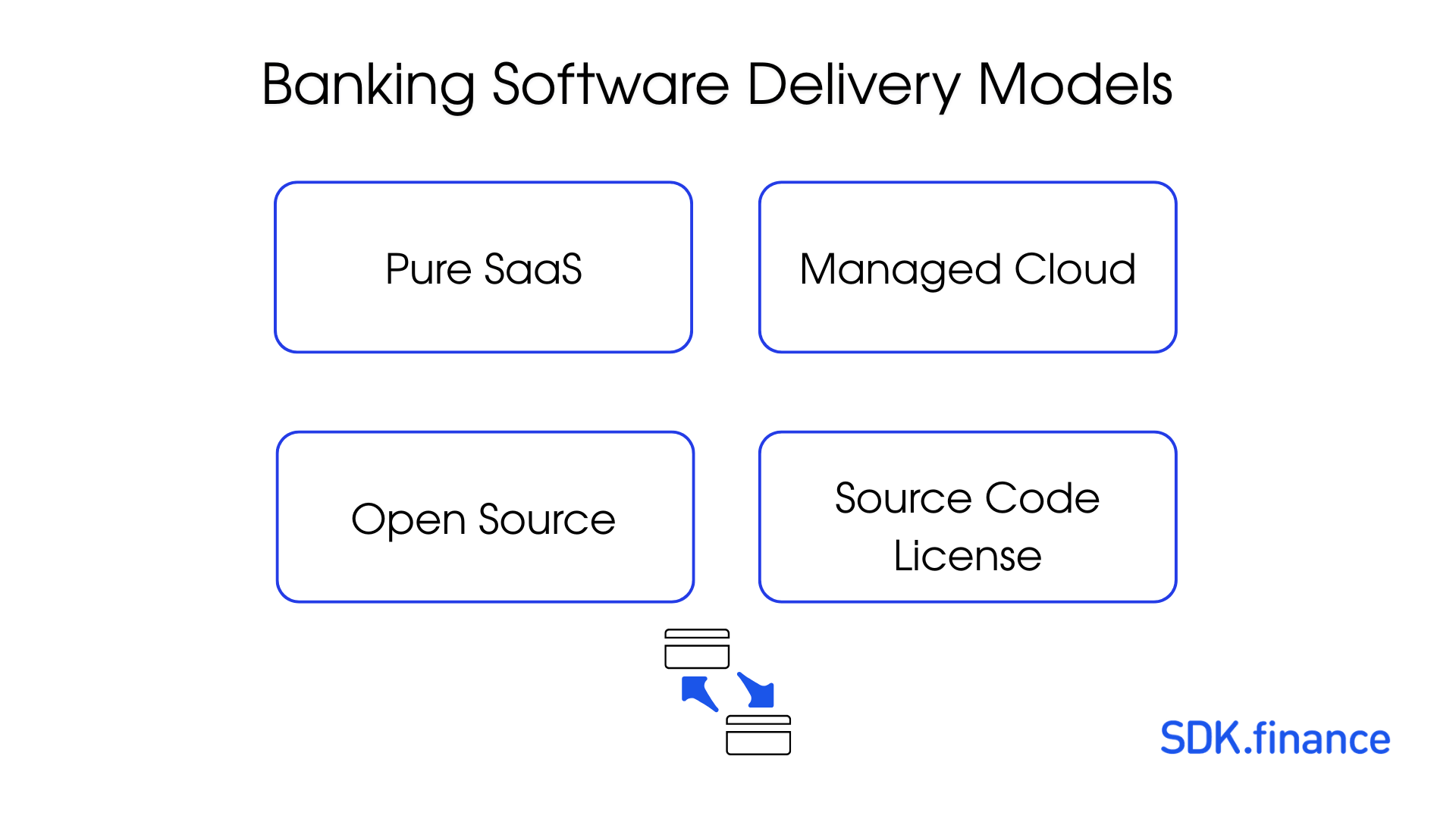
Every fintech building on third-party infrastructure makes an implicit bet on a distribution model. That bet determines what happens when the vendor raises prices, gets acquired, pivots strategy, loses a key certification, or ceases to exist. Let us examine each model on its merits.
1. Pure SaaS (Multi-Tenant)
The model: You rent access to a shared platform. The vendor hosts, operates, and controls every layer – code, data, infrastructure. You interact through APIs.
Examples: Mambu, Unit, early-stage Railsr (formerly Railsbank).
The appeal is speed. A fintech can launch a banking product in weeks rather than months. There is no infrastructure to manage, no deployment pipeline to build, no database to administer. For pre-revenue startups validating product-market fit, this speed is genuinely valuable.
The risk is total dependency. You do not control the code. You cannot inspect the transaction processing logic that your regulator may ask about. You cannot migrate away without rebuilding from scratch. Your data sits in a shared environment governed by the vendor’s security posture, not yours.
The failure modes are well-documented. Railsr, the UK-based BaaS provider, entered administration in 2023, leaving its fintech clients scrambling to find alternatives while maintaining service to their own customers. Synapse’s bankruptcy demonstrated the terminal case: when a pure SaaS BaaS provider fails, its clients do not experience a service degradation – they experience a business extinction event.
Vendor lock-in in pure SaaS is not a risk to be managed. It is a certainty to be accepted.
2. Managed Cloud (Single-Tenant SaaS)
The model: You get your own dedicated instance of the vendor’s platform, typically running in the vendor’s cloud account or a managed environment. The vendor still owns and controls the code.
Examples: Thought Machine Vault (cloud-hosted), Temenos SaaS offerings.
This is a meaningful improvement over multi-tenant SaaS. Your data is isolated. Performance is not affected by other tenants. Some vendors offer limited configuration beyond what multi-tenant allows.
But the core dependency remains. The vendor controls the source code. If Thought Machine decides to deprecate a feature you depend on, you wait for their roadmap, or you migrate. If Temenos restructures its SaaS pricing – as enterprise software vendors routinely do – your cost model changes at their discretion, not yours.
Migration from a managed cloud to an alternative is a 3- to 5-year project in most cases, with costs ranging from $1 million for smaller implementations to $50 million or more for large-scale core banking replacements. These are not estimates designed to frighten – they are drawn from industry case studies of banks migrating between core platforms.
The managed cloud model reduces operational risk compared to multi-tenant SaaS. It does not reduce strategic risk. You remain dependent on the vendor’s continued existence, continued investment, and continued alignment with your business needs.
3. Open Source
The model: The source code is freely available. You download it, deploy it, and operate it yourself. Community contributors maintain and extend it.
Examples: Apache Fineract, Mifos.
The philosophical appeal is powerful. No vendor lock-in. Full transparency. Community-driven development. For microfinance institutions in developing markets, projects like Mifos and Fineract have delivered genuine value.
The operational reality is more complex. Open-source fintech platforms typically lack enterprise compliance certifications. Achieving these certifications independently costs about $200,000 to $500,000 (total cost – not only certificator fee) or more annually, requires dedicated compliance staff, and demands ongoing audit cycles.
There is no SLA. When a critical bug surfaces at 2 AM, you file a GitHub issue and hope. The “free” in open source refers to licensing cost, not the total cost of ownership. Organizations deploying open-source fintech infrastructure routinely spend more on internal engineering, security hardening, and compliance than they would have spent licensing a commercial product.
Open source eliminates vendor lock-in. It does not eliminate risk. It transfers risk from the vendor to your engineering and compliance teams – teams that, in most fintechs, are already stretched thin.
4. Source Code License
The model: You license the full production source code of a commercially developed, tested, and certified platform. You deploy it on your own infrastructure. You modify it as needed. The vendor provides support but does not control your deployment.
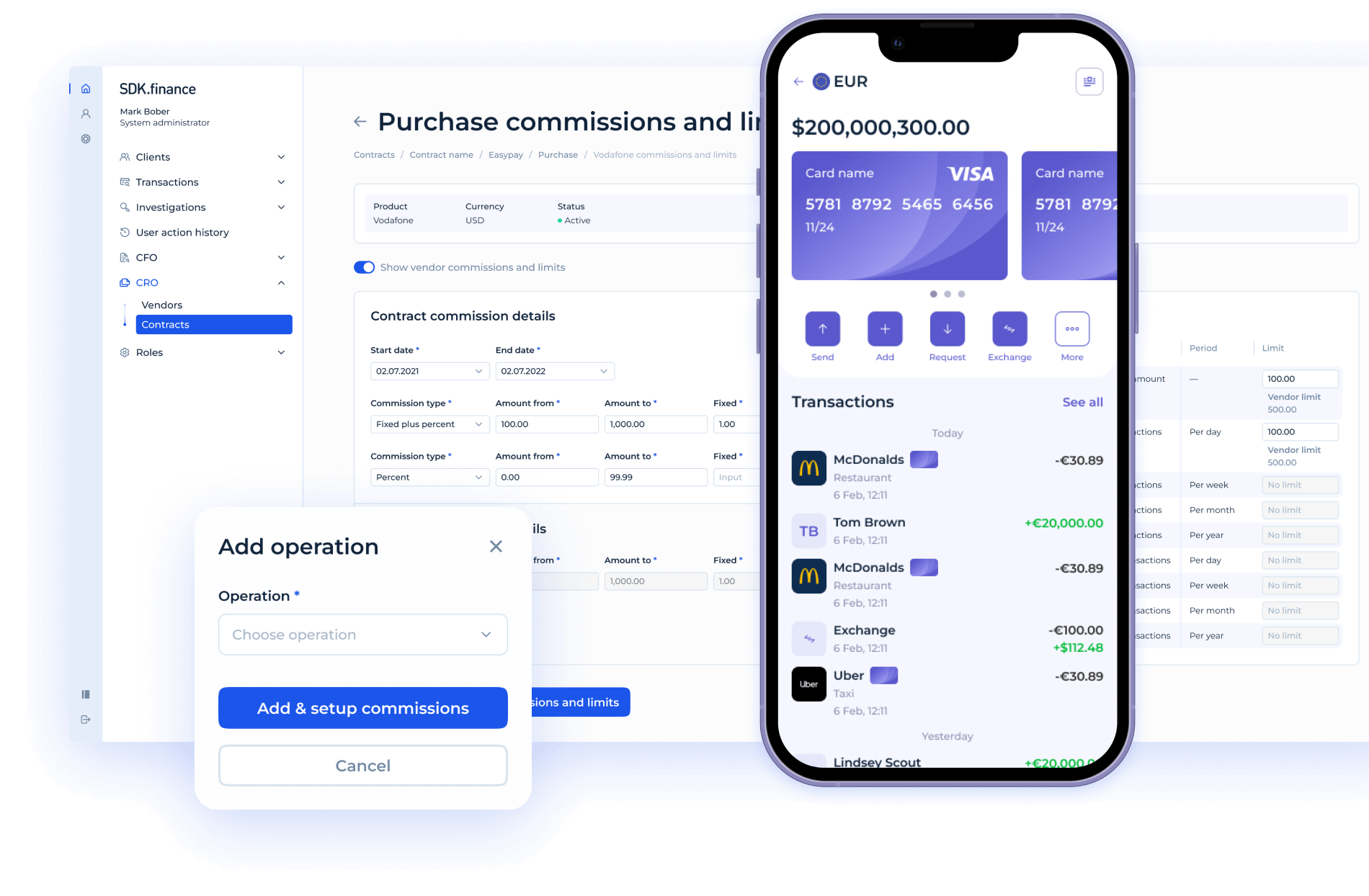
This is the model SDK.finance has operated under since 2013. Clients receive:
- The complete source code – not a framework, not a toolkit, but the same production system running in live financial environments.
- Built on Java 17 with Spring Boot, backed by PostgreSQL and MongoDB, with Apache Kafka for event streaming.
- Over 570 REST API endpoints across 60+ modules.
- Baseline throughput of 2,700+ transactions per second, horizontally scalable.
Critically, the platform ships with PCI DSS Level 1 certification and ISO 27001:2022 compliance already in place. The client inherits a certified security posture rather than building one from the ground up.
The source code license model is the only distribution model that simultaneously achieves three outcomes:
- Zero vendor dependency. If SDK.finance ceased to exist tomorrow, every client’s system would continue running. The code is theirs. The infrastructure is theirs. There is no API to go dark, no hosted service to shut down, no middleware layer to disappear.
- Full regulatory auditability. When a regulator asks, “Show me how your payment routing logic works,” the client opens the source code. There is no need to request documentation from a vendor, no need to rely on a vendor’s description of their own system, no need to trust a black box.
- Unconstrained customization. Clients modify the transaction engine, add new payment methods, integrate with local banking rails, adjust compliance rules for new jurisdictions – without submitting feature requests and waiting for a vendor’s product roadmap to align with their business needs.
Comparison Matrix
| Criterion | Pure SaaS | Managed Cloud | Open Source | Source Code License |
|---|---|---|---|---|
| Vendor lock-in risk (0 = none, 10 = total) | 9-10 | 7-8 | 0-1 | 0-1 |
| Business continuity if vendor fails | Service terminates | Difficult migration | Unaffected | Unaffected |
| Regulatory auditability | Dependent on vendor | Partially dependent | Full | Full |
| Compliance certifications (PCI DSS, ISO 27001) | Vendor’s responsibility | Vendor’s responsibility | You build from scratch | Included and transferable |
| Customization freedom | API-level only | Configuration-level | Unlimited (no support) | Unlimited (with support) |
| Time to initial launch | Weeks | Months | 6-18 months | 2-6 months |
| 5-year total cost of ownership | Medium-High (compounding fees) | High | Low license, high ops | Medium (one-time + support) |
| Data sovereignty compliance | Vendor-dependent | Partially configurable | Full control | Full control |
| Multi-jurisdiction deployment | Vendor must support | Vendor must support | Self-managed | Self-managed |
| Infrastructure choice | None | Limited | Full | Full |
| Ability to pass regulator code audit | Impossible without vendor | Difficult | Possible | Straightforward |
The pattern is clear. Open source and source code licensing both eliminate vendor lock-in. But only source code licensing combines that independence with production-grade reliability, certified compliance, and commercial support.
The Regulatory Pressure: Why This Matters Now

The Synapse collapse did not occur in a regulatory vacuum. It accelerated a series of regulatory actions that are fundamentally reshaping expectations for financial technology providers. Each of these developments increases the operational costs and compliance risks associated with dependence on opaque infrastructure.
FDIC Post-Synapse Actions (United States)
In the wake of the Synapse failure, the FDIC issued proposed rules requiring banks to maintain direct, real-time access to customer account records – eliminating reliance on middleware providers for ledger reconciliation. Banks that partner with BaaS providers must now demonstrate that they, not the middleware layer, control the source of truth for customer funds. This makes black-box BaaS architectures a direct regulatory liability.
PSD3 and PSR (European Union)
The forthcoming Payment Services Directive 3 and Payment Services Regulation tighten accountability for payment institutions. Banks and licensed payment institutions bear direct responsibility for the actions of their technology partners. Outsourcing to a SaaS provider does not outsource regulatory liability. If the regulator finds a compliance failure in the payment-processing logic, the licensed institution is accountable, whether or not it can inspect that logic.
MiCA – Markets in Crypto-Assets Regulation (European Union)
MiCA requires crypto-asset service providers to demonstrate operational resilience and transparent governance of their technology stack. Platforms must be able to explain how transactions are processed, how assets are custodied, and how compliance rules are enforced. A multi-tenant SaaS platform where the client cannot access the source code makes this demonstration structurally difficult.
DORA – Digital Operational Resilience Act (European Union)
Taking full effect in January 2025, DORA mandates that financial entities maintain operational resilience across their ICT systems, including third-party providers. Organizations must map their ICT dependencies, stress-test for vendor failure, and maintain exit strategies. DORA essentially requires you to have a plan for exactly the scenario that Synapse’s clients did not plan for.
FIDA – Framework for Financial Data Access (European Union)
FIDA expands the scope of open finance, requiring financial institutions to share customer data across a wider range of financial products. Implementing FIDA compliance requires deep integration with core transaction systems – the kind of integration that is straightforward with source code access and difficult or impossible through a SaaS API alone.
EU AI Act
As financial institutions deploy AI for credit scoring, fraud detection, and customer risk assessment, the EU AI Act requires that high-risk AI decisions be explainable and auditable. If your AI models operate on transaction data processed by a black-box SaaS platform, the auditability chain is broken at the infrastructure level.
SAMA Regulations (Saudi Arabia)
The Saudi Arabian Monetary Authority requires that financial data generated within the Kingdom remain within the Kingdom. This data sovereignty mandate effectively disqualifies any BaaS model where the vendor controls data residency decisions. Organizations must deploy on local infrastructure – a requirement that is trivially met with source code access and difficult to meet with SaaS platforms that operate in centralized cloud regions.
The regulatory direction is unambiguous. Across jurisdictions, regulators are demanding that financial institutions control, audit, and operate their own technology infrastructure. Every regulatory development listed above increases the cost of relying on infrastructure you do not own.
Three Scenarios, Four Outcomes
Theory is useful. Scenarios are more persuasive. Consider how each distribution model responds to three situations drawn from real events.
Scenario A: Your BaaS Vendor Goes Bankrupt
This is the Synapse scenario. Your vendor files for bankruptcy. Its systems begin degrading, then go offline.
- Pure SaaS: Your service stops. Customer funds may be inaccessible. You rebuild on a new platform from scratch – a process measured in months, during which your customers have no service.
- Managed Cloud: Your instance may continue running temporarily, but you have no access to the source code, no ability to patch, and a ticking clock before infrastructure contracts expire. Migration takes 12-36 months.
- Open Source: Your system is unaffected. You continue operating. However, you absorb all future maintenance, security patching, and compliance burden with no commercial support.
- Source Code License: Your system is unaffected. You continue operating with full source code, existing compliance certifications, and the option to engage alternative support providers. Business continuity is complete.
Scenario B: A Regulator Demands a Code Audit of Your Payment Logic
Your licensing authority – whether the FCA, BaFin, MAS, or SAMA – requests a detailed audit of how your system processes payments, applies fees, and handles settlement.
- Pure SaaS: You ask your vendor. The vendor provides documentation of varying completeness and accuracy. The regulator may or may not accept a vendor-authored description of the vendor’s own system.
- Managed Cloud: Similar to pure SaaS. You may have slightly better documentation, but you cannot show the actual code.
- Open Source: You provide the source code directly. However, if you have modified it significantly (which is common), you must demonstrate that your modifications maintain compliance – without the backing of a certification authority.
- Source Code License: You provide the source code directly, backed by existing PCI DSS Level 1 and ISO 27001:2022 certifications. The regulator sees exactly what runs in production, and the certifications provide independent validation of security and operational controls.
Scenario C: You Need to Launch in a New Country with Data Residency Requirements
Your business expands into a market – Saudi Arabia, Indonesia, Nigeria – where regulators require that financial data be stored and processed within national borders.
- Pure SaaS: If your vendor does not operate infrastructure in that country, you cannot launch. Your expansion timeline is now tied to your vendor’s infrastructure roadmap.
- Managed Cloud: Possible if the vendor supports deployment in the target region. If not, you wait or you find a new vendor for that market – fragmenting your technology stack.
- Open Source: You deploy on local infrastructure yourself. Feasible, but you bear the full burden of infrastructure management, security, and compliance in a new jurisdiction.
- Source Code License: You deploy on local infrastructure – AWS, Azure, Google Cloud, Oracle, IBM, Huawei Cloud, or on-premises data centers. The same codebase, the same certifications, the same operational procedures. Multi-jurisdiction deployment is an infrastructure decision, not a vendor negotiation.
The De-Risking Argument
Risk management in fintech is typically discussed in terms of credit risk, fraud risk, and compliance risk. Vendor risk – the risk that your technology provider becomes a liability rather than an asset – deserves equal attention.
Source code access is, fundamentally, an insurance policy against vendor risk. Consider the coverage it provides:
- Continuity insurance. Your system runs regardless of the vendor’s financial health, strategic direction, or corporate structure. No bankruptcy, acquisition, or pivot can shut down your operations.
- Compliance insurance. PCI DSS Level 1 and ISO 27001:2022 certification transfers with the code. You are not starting from zero when a regulator asks for evidence of security controls. You are presenting a system that has already passed the most rigorous industry audits.
- Infrastructure insurance. With support for deployment across AWS, Azure, Google Cloud, Oracle Cloud, IBM Cloud, Huawei Cloud, and on-premises environments, there is no infrastructure lock-in layered on top of the software. If one cloud provider changes its pricing, its terms, or its regional availability, you move.
- Innovation insurance. With 570+ API endpoints across 60+ modules – covering accounts, payments, cards, KYC, compliance, lending, and merchant services – the platform is production-ready from day one. But when the market demands something the platform does not yet support, you build it. You do not submit a feature request and hope it aligns with someone else’s quarterly planning cycle.
SDK.finance has operated this model since 2013 – over thirteen years of continuous development and refinement. The platform currently processes payment traffic for clients, including one that handles 75% of national payment volume. This is not a framework awaiting its first production deployment. It is battle-tested infrastructure.
For organizations at different stages, the path forward need not be binary. SDK.finance offers a dual licensing model: start with SaaS for speed, then graduate to source code when independence becomes the priority. The migration is by design, not by crisis.
Conclusion: Control is the New Competitive Advantage
For the past decade, the fintech infrastructure market was defined by a single question: who has the best features? The vendor with the most payment methods, the fastest onboarding, the slickest dashboard won the deal.
That era is ending.
The Synapse collapse, the Railsr administration, and the regulatory response they provoked have introduced a new question: who gives me the most control?
Control over the code that processes my customers’ money. Control over the infrastructure that stores their data. Control over the compliance posture that satisfies my regulators. Control over the roadmap that determines my product’s future.
In a market where regulators across three continents are simultaneously tightening requirements for operational resilience, data sovereignty, and technology accountability, the organizations that thrive will be those that own their infrastructure.
Don’t rent it. Don’t borrow it. Own it.
Pure SaaS offers speed at the cost of dependency. Managed cloud offers isolation at the cost of control. Open source offers freedom at the cost of support and certification. Only source code licensing offers the full picture: independence, auditability, certified compliance, commercial support, and the freedom to deploy anywhere, customize anything, and survive any vendor scenario.
Owning your fintech infrastructure is not a luxury. In the regulatory and competitive landscape of 2026 and beyond, it is a requirement for survival.