In the age of contactless payments, businesses and consumers need a payment service provider (PSP) to process online transactions. Currently, the projected transaction value for PSPs is $6.68 trillion — highlighting the ongoing shift to digital PSPs.
But what is a PSP and what do PSPs do?
In this article, we define the working principles of a standard payment service provider. Follow along as we explore the key characteristics of a reputable payment solutions provider.
All aboard!
What is a payment service provider?
A payment service provider is a company that offers online payment solutions to merchants — businesses, banks, and other financial and e-commerce institutions.
In essence, PSPs combine multiple merchants under the same umbrella to reduce transaction fees and fine-tune payments.
PSP services include online banking, credit and debit cards, e-wallets, and peer-to-peer payments.
How does a payment service provider work?
Before dissecting the working principles of PSPs, let’s take a detour to understand PSP payments.
So, what is PSP payment?
A PSP payment refers to any transaction between two businesses or customers — or between a customer and a business.
But you need a medium to process these payments, right?
Yes. All PSP payments go through a payment processing software.
And what is payment processing software?
A payment processing software is any application (probably an API or SDK) that aggregates, authenticates, and approves B2B, P2P, and B2C transactions. Most companies offer this application as a PaaS (payment as a service).
With a better understanding of basic terms, let’s double back to the PSP mode of operation.
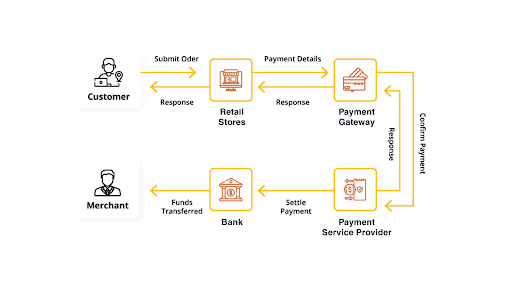
When processing a payment, the payment service provider acts as the intermediary to both parties: side A (payer) and side B (acquiring and issuing banks).
Let’s say you (side A) swipe your card at checkout or point of sale (POS); the PSP application receives an encrypted request to execute the transaction through the payment gateway (more on that later).
To confirm the request, you must provide a PIN code or other form of verification.

Source: Magestore
The PSP software relays the request to the issuing bank to authenticate the card information. After approval, the acquiring bank compares the requested transaction amount to the amount of money in the payer’s ledger. If the operation is successful, the transaction clears; otherwise, you get a “transaction declined” response.
Payment gateway vs. payment service provider
As mentioned earlier, a payment gateway handles the encrypted transfer of information between side A and side B — and that makes it similar to a payment service provider, right?
Wrong!
In PSP finance, payment gateways are only part one part of the entire process.
So what is a gateway provider, really?
A gateway provider is a company that uses gateway technology and card-reading devices to authorize and accept payment details.
Source: Magestore
Once the payment is “cleared” on both ends, the gateway hands over the mantel to the issuing and acquiring banks.
7 key features to identify a reliable payment service provider
As PSP banking peaks in popularity, more online payment service providers enter the market. And like in any saturated sector, choosing the right service provider for your business becomes a critical challenge.
Go for the brand-name service or choose the cheaper alternative?
We’ve done the research and identified the core features to consider when choosing a payment service provider.
Here they are…
Machine learning and artificial intelligence capabilities
Any forward-thinking company must embrace new technologies to stay relevant in the ever-changing socio-economic landscape — and it doesn’t get much better than AI and machine learning.
AI-based payment service providers offer smart solutions for customers and businesses to perform transactions without hiccups. With machine learning features, you can monitor consumer behavior and irregular payment patterns, especially when dealing with fraud.
Anti-fraud protection
Top-of-the-pile payment service providers use machine learning algorithms to spot discrepancies in online transactions. As a result, they can detect fraudulent transactions and honey pots that could affect your clients.
In extreme cases, the PSP can block the suspicious account temporarily until you investigate and clear the owner.
PSP reputation
Since the market is overflowing with low-grade PSPs, sticking with household names is the safest bet.
Companies like Venmo, PayPal, Stripe, and Braintree provide tested-and-trusted payment services to their users. And since the top dogs are in competition, they only offer premium quality solutions to outperform their rivals.
Not only that, but you should also read user reviews and studies into the practices of any PSP before choosing them. Why? This research will show you their transaction rejection rate and other potential red-flag technical issues.
Supported payments
When choosing a PSP, always confirm the range of payments they provide. For example, some PSP are location-restricted, limiting the scope of transactions you can conduct with your global clients.
Case in point: Vipps, a Norwegian PSP, only works in Norway.
Although this issue might not be a problem for local businesses, large corporations will struggle to perform international transactions using this app.
Apart from that, some payment solutions providers limit the acceptable card associations to VISA and Mastercard. Alternatively, you can find PSPs that accept multiple payment methods, including cryptocurrencies.
Mobile user experience
Here is the thing; experts from TechJury have ruled that over 69% of users buy goods on their mobile devices, of which 83% expect a flawless experience.
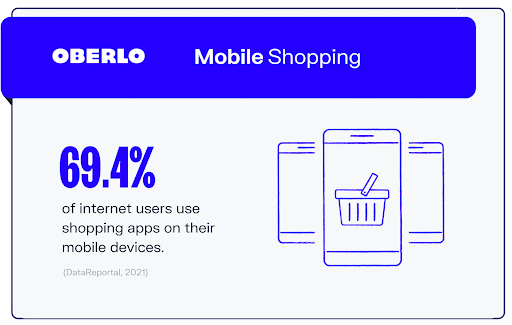
Source: Oberlo
Although maintaining a consistent experience across all platforms is a healthy recommendation, no one will blame you for prioritizing the mobile experience.
To make mobile browsing a breeze, choose PSP mobile versions that provide SMS verification, QR codes, native integration (if necessary), and hitch-free checkout.
SDK.finance provides core banking infrastructure with ledger, payments, wallets, ready applications and flexible deployment options
Book a demoCustomer support
As part of the customer experience, any platinum-grade PSP software should have round-the-clock support for users.
Apart from being an industry standard, you need to assist customers trying to navigate rejected payments or limited transactions. And in cases of suspected fraud, the PSP should help you evaluate and block suspicious businesses and practices.
Transaction and subscription fees
Every PSP has a unique subscription model — and the transaction fees differ based on the services they offer.
So when choosing a payment service provider, factor in the fees they charge per transaction; some PSPs collect percentages for every transaction (or thousand transactions).
And the fee per transaction depends on the subscription model you choose. Here are the standard PaaS subscription plans:
- Pay-per-use — pay for every instance.
- Pay-as-you-go — the price changes alongside your business.
- Periodicals — monthly, quarterly, annually.
- Flat rate — every user pays the same amount.
Large enterprises can afford the cost of these services, but small businesses must cut their spending to a few parameters:
- Reputation
- Available features
- Company (business) size
- Security
- Duration
SDK.finance Platform provides a powerful fees management section that helps you to focus on maximizing your revenue. Watch our demo video to explore how to set up flexible fee structures for each vendor, optimizing your revenue potential:
5 factors to consider when creating your payment service provider software
If you don’t think Stripe and PayPal cut it for your business, you could always develop your own payment service provider from scratch — or from an existing API.
Assuming your business or digital retail bank decides to create an in-house custom payment service provider, here are a few things to consider:
Regulation and compliance
Every transaction service must comply with established industry regulations like the Payment Card Industry Data Security Standard (PCI DSS). Otherwise, customers can’t use the service for transactions.
Identification
To improve the security of transactions, you must include additional identification modules like fingerprinting and facial recognition. But before doing so, ensure that the modules comply with the General Data Protection Regulation (GDPR).

Source: Security Metrics
Yes, those finicky compliance regulations!
While PCI DSS protects payment data, GDPR covers every other thing.Hosting
You need a dedicated server to store payment and user data. Choose a locally-hosted or cloud-based server for your PSP depending on the transaction volume, frequency, and existing software.
Scalability
The payment service platform should have a flexible and adaptable infrastructure that grows with your business.
API integration
Choose a developer-friendly and easily-customizable API for your payment provider software. And most importantly, ensure that the API integration enables a hitch-free user journey, from account creation to billing.
Conclusion
As the era of contactless payments continues to materialize, payment service providers are stepping up to new consumer and business demands.
But it all comes down to choosing the right PSP for your business. You could always use one of the trademark brands that suit your company’s objectives. Alternatively, you can buy a bespoke payment solution software that you can adjust as you wish.
Contact us to discuss how our fintech development expertise, paired with a ready-to-go payment core solution, can help you create a PCI-compliant payment product right away.
References
- How to Choose a Payment Service Provider
- 64 Key Online Payments Statistics: 2020/2021 Market Share & Data Analysis – Financesonline.com
- 20 Payment Method Statistics For Merchants To Keep In Mind
- What is a Payment Gateway and How Does It Work?
- Payment Gateway Definition
- What Are Payment Service Providers? – Insights | Worldpay from FIS
- What Are Payment Service Providers?
- What Percentage of Internet Traffic Is Mobile in 2021?
- Official PCI Security Standards Council Site – Verify PCI Compliance, Download Data Security and Credit Card Security Standards
- PCI vs. GDPR: What’s the Difference?